Common Cyber Attacks Explained: Types, Examples & Prevention in 2026
In January 2026, cyber threats continue to evolve rapidly, with attacks becoming more sophisticated due to AI advancements and widespread digital reliance. Cyber attacks cost the global economy trillions annually, affecting individuals, businesses, and governments. Understanding the most common types is crucial for protection. This comprehensive guide—over 1,900 words—explains the top cyber attacks, how they work, real-world examples, their impacts, and practical prevention methods. Whether you're a homeowner securing smart devices or a business leader safeguarding data, this article equips you with essential knowledge in today's threat landscape.
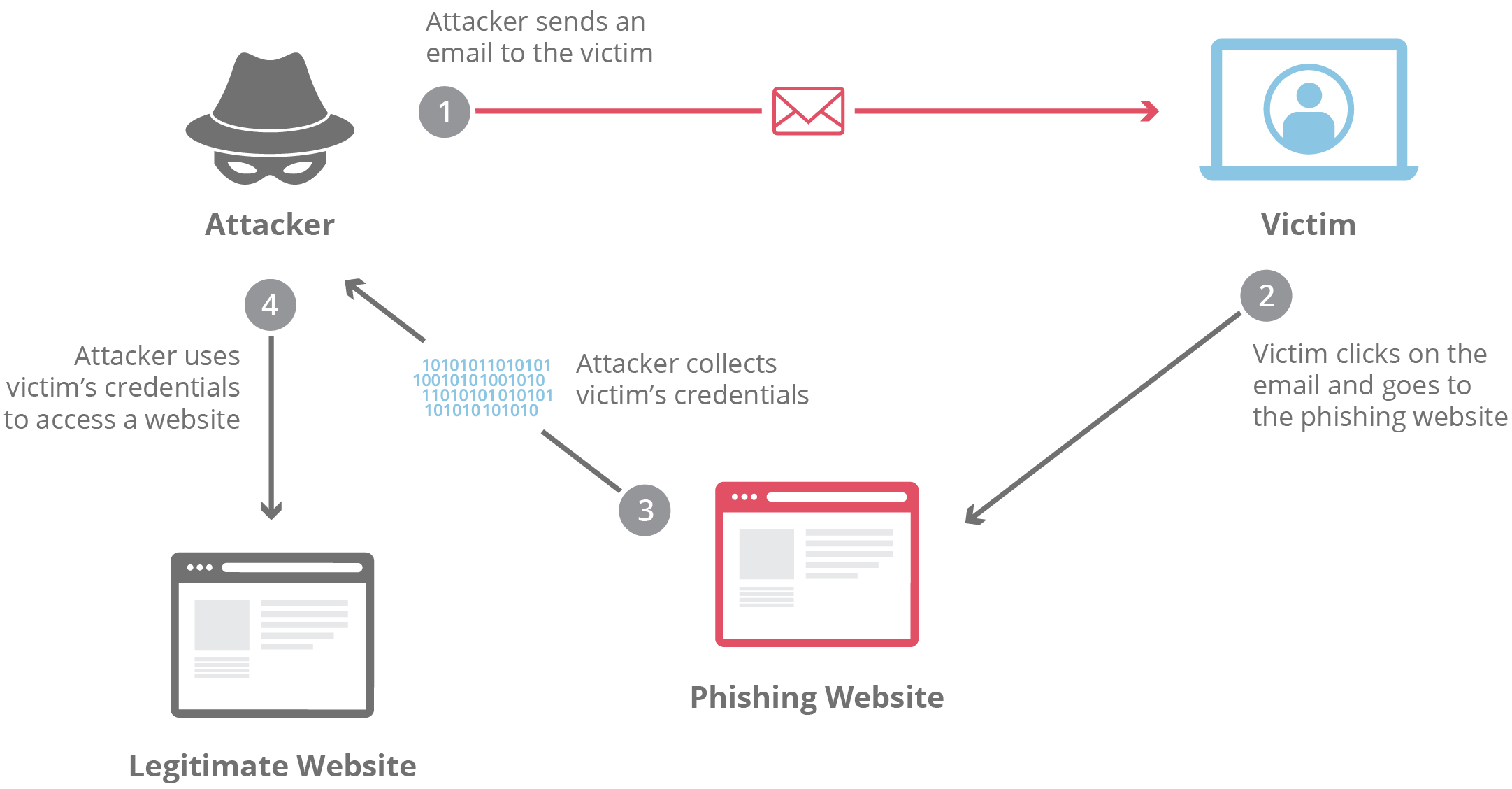
1. Phishing Attacks: The Most Prevalent Social Engineering Threat
Phishing is a type of cyber attack where attackers impersonate trustworthy entities to trick victims into revealing sensitive information, such as login credentials, credit card details, or personal data. Typically delivered via email, SMS (smishing), or voice calls (vishing), phishing exploits human psychology rather than technical vulnerabilities.
In 2026, AI-generated phishing emails are hyper-realistic, mimicking exact writing styles and including deepfake elements. Spear-phishing targets specific individuals with personalized information gathered from social media.
How it works: Attackers send fraudulent messages with urgent calls to action, linking to fake websites that capture entered data.
Real-world example: The 2024 Twitter (now X) breach began with spear-phishing employees, leading to high-profile account hijacks.
Impact: Credential theft leads to account takeovers, financial fraud, and data breaches.
Prevention: Use email filters, enable multi-factor authentication (MFA), verify sender addresses, and educate users via training simulations.
2. Ransomware: Encrypting Data for Ransom
Ransomware is malicious software that encrypts victims' files or systems, demanding payment (usually cryptocurrency) for decryption keys. Modern variants like Ransomware-as-a-Service (RaaS) lower barriers for attackers.
In 2026, double-extortion tactics prevail: encrypting data and threatening to leak it.
How it works: Delivered via phishing, drive-by downloads, or exploited vulnerabilities; once executed, it encrypts files and displays a ransom note.
Real-world example: The 2021 Colonial Pipeline attack by DarkSide caused fuel shortages across the US, with a $4.4 million ransom paid.
Impact: Operational downtime, financial losses, and reputational damage; healthcare and critical infrastructure are prime targets.
Prevention: Regular offline backups, patch management, endpoint detection tools, and zero-trust architectures.


3. Distributed Denial-of-Service (DDoS) Attacks: Overwhelming Targets
DDoS attacks flood a target server, website, or network with traffic from multiple sources (often botnets), making it unavailable to legitimate users.
In 2026, volumetric attacks exceed terabits per second, amplified by IoT devices.
How it works: Botnets send massive requests; amplification techniques (e.g., DNS) multiply traffic.
Real-world example: The 2016 Mirai botnet attacked Dyn, disrupting major sites like Twitter and Netflix.
Impact: Service outages, lost revenue, and eroded customer trust.
Prevention: CDN services (e.g., Cloudflare), rate limiting, and traffic scrubbing.
4. Malware: Versatile Malicious Software
Malware encompasses viruses, worms, trojans, spyware, and adware designed to harm or exploit systems.
AI-powered polymorphic malware evades detection by changing code signatures.
How it works: Infected via downloads, attachments, or vulnerabilities; performs actions like data theft or system control.
Real-world example: Emotet banking trojan stole millions before its 2021 takedown.
Prevention: Antivirus software, safe browsing habits, and regular updates.
5. Man-in-the-Middle (MitM) Attacks: Eavesdropping on Communications
MitM attacks intercept communication between two parties without their knowledge, allowing data theft or alteration.
Common on unsecured Wi-Fi; ARP spoofing or SSL stripping are techniques.
Example: Public Wi-Fi attacks stealing login credentials.
Prevention: Use VPNs, HTTPS, and certificate pinning.
6. Other Emerging Threats in 2026
- SQL Injection: Injecting malicious code into databases via input fields.
- Zero-Day Exploits: Attacking unpatched vulnerabilities.
- Supply Chain Attacks: Compromising third-party vendors (e.g., SolarWinds 2020).
- AI-Driven Attacks: Deepfakes for social engineering or automated vulnerability scanning.
General Prevention Strategies for 2026
Adopt a layered defense:
- Implement MFA everywhere.
- Regular software updates and patching.
- Employee training and awareness programs.
- Advanced tools: Firewalls, intrusion detection, EDR.
- Incident response plans and cyber insurance.
- Zero-trust models: Verify everything.
Conclusion
Cyber attacks in 2026 are more frequent and advanced than ever, driven by financial motives, geopolitics, and technological progress. From phishing deceiving users to ransomware crippling organizations, these threats underscore the need for vigilance. By understanding common attacks, learning from real examples, and applying robust prevention measures, individuals and businesses can significantly reduce risks. Cybersecurity is a shared responsibility—stay informed, invest in defenses, and foster a security-first culture. In a hyper-connected world, proactive protection is the best defense against evolving cyber threats.